前言
之前开启了docker的2375 Remote API,接到公司安全部门的要求,需要启用授权,翻了下官方文档
Protect the Docker daemon socket
启用TLS
在docker服务器,生成CA私有和公共密钥
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24 |
$ openssl genrsa -aes256 -out ca-key.pem 4096
Generating RSA private key, 4096 bit long modulus
............................................................................................................................................................................................++
........++
e is 65537 (0x10001)
Enter pass phrase for ca-key.pem:
Verifying - Enter pass phrase for ca-key.pem:
$ openssl req -new -x509 -days 365 -key ca-key.pem -sha256 -out ca.pem
Enter pass phrase for ca-key.pem:
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:
State or Province Name (full name) [Some-State]:Queensland
Locality Name (eg, city) []:Brisbane
Organization Name (eg, company) [Internet Widgits Pty Ltd]:Docker Inc
Organizational Unit Name (eg, section) []:Sales
Common Name (e.g. server FQDN or YOUR name) []:$HOST
Email Address []:Sven@home.org.au |
有了CA后,可以创建一个服务器密钥和证书签名请求(CSR)
$HOST 是你的服务器ip
|
1
2
3
4
5
6
7 |
$ openssl genrsa -out server-key.pem 4096
Generating RSA private key, 4096 bit long modulus
.....................................................................++
.................................................................................................++
e is 65537 (0x10001)
$ openssl req -subj "/CN=$HOST" -sha256 -new -key server-key.pem -out server.csr |
接着,用CA来签署公共密钥:
|
1
2
3 |
$ echo subjectAltName = DNS:$HOST,IP:$HOST:127.0.0.1 >> extfile.cnf
$ echo extendedKeyUsage = serverAuth >> extfile.cnf |
生成key:
|
1
2
3
4
5
6 |
$ openssl x509 -req -days 365 -sha256 -in server.csr -CA ca.pem -CAkey ca-key.pem \\
-CAcreateserial -out server-cert.pem -extfile extfile.cnf
Signature ok
subject=/CN=your.host.com
Getting CA Private Key
Enter pass phrase for ca-key.pem: |
创建客户端密钥和证书签名请求:
|
1
2
3
4
5
6
7 |
$ openssl genrsa -out key.pem 4096
Generating RSA private key, 4096 bit long modulus
.........................................................++
................++
e is 65537 (0x10001)
$ openssl req -subj '/CN=client' -new -key key.pem -out client.csr |
修改extfile.cnf:
|
1 |
echo extendedKeyUsage = clientAuth > extfile-client.cnf |
生成签名私钥:
|
1
2
3
4
5
6 |
$ openssl x509 -req -days 365 -sha256 -in client.csr -CA ca.pem -CAkey ca-key.pem \\
-CAcreateserial -out cert.pem -extfile extfile-client.cnf
Signature ok
subject=/CN=client
Getting CA Private Key
Enter pass phrase for ca-key.pem: |
将Docker服务停止,然后修改docker服务文件
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19 |
[Unit]
Description=Docker Application Container Engine
Documentation=http://docs.docker.io
[Service]
Environment="PATH=/opt/kube/bin:/bin:/sbin:/usr/bin:/usr/sbin"
ExecStart=/opt/kube/bin/dockerd --tlsverify --tlscacert=/root/docker/ca.pem --tlscert=/root/docker/server-cert.pem --tlskey=/root/docker/server-key.pem -H unix:///var/run/docker.sock -H tcp://0.0.0.0:2375
ExecStartPost=/sbin/iptables -I FORWARD -s 0.0.0.0/0 -j ACCEPT
ExecReload=/bin/kill -s HUP $MAINPID
Restart=on-failure
RestartSec=5
LimitNOFILE=infinity
LimitNPROC=infinity
LimitCORE=infinity
Delegate=yes
KillMode=process
[Install]
WantedBy=multi-user.target |
然后重启服务
|
1
2 |
systemctl daemon-reload
systemctl restart docker.service |
重启后查看服务状态:
|
1
2
3
4 |
systemctl status docker.service
● docker.service - Docker Application Container Engine
Loaded: loaded (/etc/systemd/system/docker.service; enabled; vendor preset: enabled)
Active: active (running) since Thu 2019-08-08 19:22:26 CST; 1 min ago |
已经生效。
使用证书连接:
复制ca.pem,cert.pem,key.pem三个文件到客户端
|
1 |
docker --tlsverify --tlscacert=ca.pem --tlscert=cert.pem --tlskey=key.pem -H=$HOST:2375 version连接即可 |
docker-java 启用TLS
项目里使用docker的java客户端docker-java调用docker,为了支持TLS,在创建客户端时,需要增加TLS设置。
首先将ca.pem cert.pem key.pem这三个文件拷贝到本地,例如E:\\\\docker\\\\",
然后DefaultDockerClientConfig里withDockerTlsVerify设为true,并设置certpath为刚拷贝的目录。
|
1
2
3
4
5
6
7
8
9 |
DefaultDockerClientConfig.Builder builder =
DefaultDockerClientConfig.createDefaultConfigBuilder()
.withDockerHost("tcp://" + server + ":2375")
.withApiVersion("1.30");
if (containerConfiguration.getDockerTlsVerify()) {
builder = builder.withDockerTlsVerify(true)
.withDockerCertPath("E:\\\\docker\\\\");
}
return DockerClientBuilder.getInstance(builder.build()).build() |
大工搞定。
总结
以上就是这篇文章的全部内容了,希望本文的内容对大家的学习或者工作具有一定的参考学习价值,谢谢大家对快网idc的支持。
原文链接:https://www.cnblogs.com/xiaoqi/p/docker-tls.html
相关文章
- 刀片服务器与机架服务器的区别介绍 2025-05-27
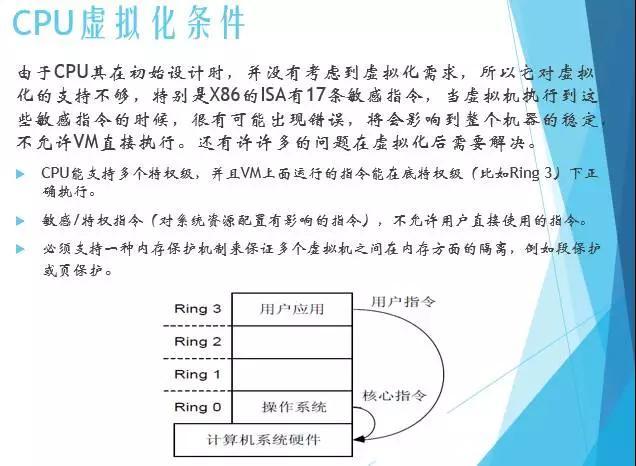
- 服务器虚拟化技术深度科普 2025-05-27
- 服务器租用价格怎么计算?服务器租用多少钱一年? 2025-05-27
- 云服务器的“弹性”体现在哪些方面? 2025-05-27
- 刀片服务器是什么 刀片服务器的主要特点 2025-05-27
- 2025-07-10 怎样使用阿里云的安全工具进行服务器漏洞扫描和修复?
- 2025-07-10 怎样使用命令行工具优化Linux云服务器的Ping性能?
- 2025-07-10 怎样使用Xshell连接华为云服务器,实现高效远程管理?
- 2025-07-10 怎样利用云服务器D盘搭建稳定、高效的网站托管环境?
- 2025-07-10 怎样使用阿里云的安全组功能来增强服务器防火墙的安全性?
快网idc优惠网
QQ交流群
-
2025-05-25 32
-
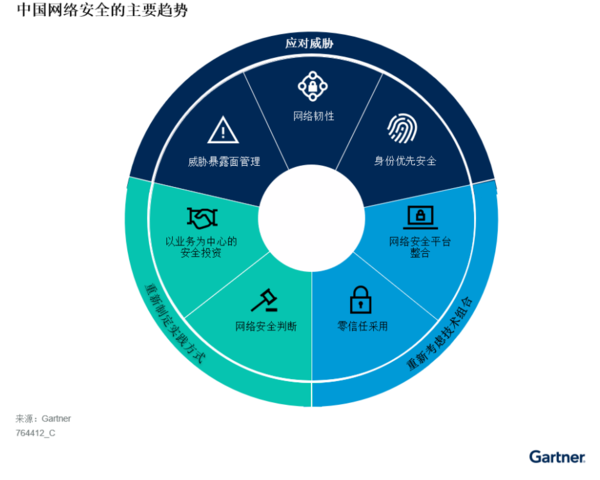
Gartner发布网络安全重要趋势,包括威胁暴露面管理、零信任采用等
2025-05-26 67 -
2025-05-25 90
-
服务器端包含、嵌入技术SSI(Server SideInc lude)详解
2025-05-27 36 -
2025-05-27 86