一、概述
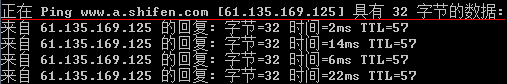
现在来搞定DNS域名解析,其实这是前面一篇文章C++实现Ping里面的遗留问题,要干的活是ping的过程中画红线的部分:
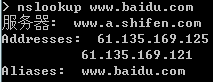
cmd下域名解析的命令是nslookup,比如“nslookup www.baidu.com”的结果如下:
其中,Address返回的就是www.baidu.com对应的IP地址,这个可能有多个
Alias指别名,也就是说www.baidu.com是www.a.shifen.com的别名,而www.a.shifen.com则是www.baidu.com的规范名(Canonical Name,CName),具体参考RFC1035 3.2.2 & wikipedia
二、实现结果预览
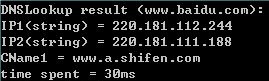
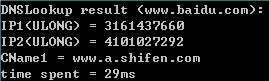
先看一下最终搞成了什么样子
输入:域名字符串
输出:IP列表、CName列表、DNS查询所用时间
三、相关技术
3.1、UDP or TCP ? (RFC1035 4.2)
UDP:DNS查询和回复采用低开销高性能的UDP,端口号为53。
TCP:辅助DNS服务器从主DNS服务器拉取最新数据时,采用可靠的TCP传输,端口号也为53。
我们这里做DNS查询采用UDP,53端口。
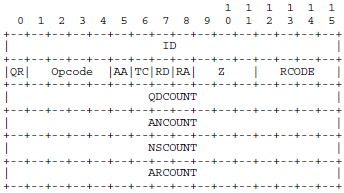
3.2、DNS查询/回复包头部解析 (RFC1035 4.1.1)
重点介绍一下我们关心的部分:
ID(16bits):标识符,一般填入本进程的标识符
QR(1bits):标志位,查询包为0,回复包为1
Opcode(4bits):查询的种类,标准查询为0
QDCOUNT(16bits):DNS查询/回复包数据部分Question字段的个数
ANCOUNT(16bits):DNS查询/回复包数据部分Answer字段的个数
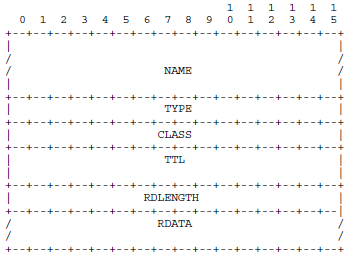
3.2、DNS查询/回复包数据部分解析 (RFC1035 4.1.2 & 4.1.3)
查询/回复包的数据部分依次为QDCOUNT个Question字段、ANCOUNT个Answer字段….
对于任意字段,其格式如下:
Name(不定长):域名,这部分的格式比较复杂,后面单独说。
TYPE(16bits):查询类型/回复包RDATA类型,比如TYPE=1表示主机IP地址、TYPE=5表示CNAME,详见RFC1035 3.2.2
CLASS(16bits):类,一般情况下CLASS=1表示Internet,详见RFC1035 3.2.4
TTL(32bits,仅回复包):生存时间
RDLENGTH(16bits,仅回复包):RDATA部分的字节数
RDATA(不定长,仅回复包):资源数据,具体格式取决于TYPE和CLASS,比如TYPE=1、CLASS=1时,RDATA为四个字节的IP地址
3.3、Name解析&消息压缩
3.3.1、一般格式 (RFC1035 4.1.2)
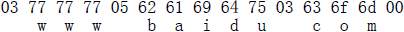
标签内容长度(1个字节) + 标签内容,以标签内容长度0作为Name的结束符,例如:
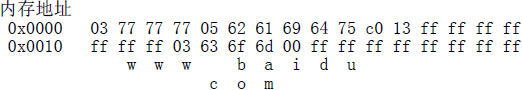
3.3.2、消息压缩格式 (RFC1035 4.1.4)
如果标签内容长度的二进制前两位是11,则表示消息压缩。
此时,标签内容长度1个字节+后面的1个字节一共16位,后14位表示相对DNS包起始地址的偏移(Byte),例如:
上述例子中,DNS包起始地址为0x0000,c0 13的二进制为11000000 00010003,即跳转偏移为0x13个字节,对应的数据为03 63 6f 6d 00。
RFC1035中规定,支持的消息压缩规则为:
①以内容长度0结尾的标签序列
②偏移指针
③标签序列+偏移指针
也就是说,Name的消息压缩要求偏移指针必须在Name的尾部,且不支持同一级存在多个偏移指针(偏移指针序列),
但Name的消息压缩支持嵌套的偏移指针,即指针指向的偏移位置仍然是以偏移指针结尾的数据
四、代码实现